How Fortinet Firewall Multi-Layered Security Keeps Australian Schools Safe from Cyber Threats
How Fortinet Firewall Multi-Layered Security Keeps Australian Schools Safe from Cyber Threats
Australian schools are facing a sharp rise in cyber threats, from phishing campaigns targeting staff to ransomware attacks that can disrupt learning for weeks. A modern Fortinet firewall is no longer just a network device it is the foundation of a multi-layered security strategy that protects users, devices, applications, and cloud platforms.
For schools across Australia, the challenge is clear: safeguard sensitive student data while enabling flexible, cloud-first learning environments. This is where Fortinet’s integrated Security Fabric, combined with Accucom’s education IT expertise, delivers measurable value.
Why a Fortinet Firewall Is Critical in Education IT
A Fortinet firewall acts as the first line of defence between your school network and external threats. Unlike traditional firewalls that simply filter traffic, Fortinet’s next-generation firewall (NGFW) provides deep packet inspection, application control, intrusion prevention, and SSL inspection in a single platform.
In a school environment, this means
- Blocking malicious traffic before it enters the network,
- Preventing ransomware from spreading laterally,
- Inappropriate content for compliance and child safety, and
- Securing remote access for staff and students.
However, perimeter protection alone is not enough. Schools today rely heavily on Microsoft 365, cloud-based learning platforms, BYOD programs, and hybrid learning models. Security must extend beyond the edge of the network.
Fortinet’s Security Fabric enables this broader protection.
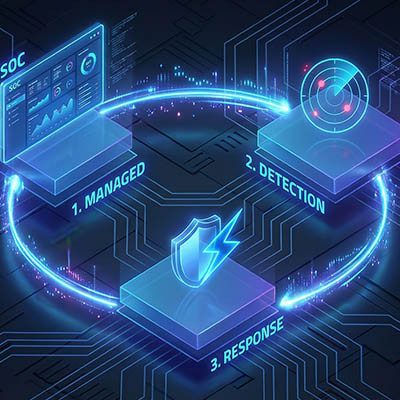
How Fortinet Firewall Supports Multi-Layered Security in Schools
Multi-layered security, often referred to as defence-in-depth, ensures that if one layer fails, others remain in place to prevent compromise. Fortinet’s integrated Security Fabric connects firewall, endpoint, wireless, switching, and cloud security into a single coordinated system.
Network Layer Protection
At the core, the Fortinet firewall protects the school’s WAN and LAN infrastructure. It detects intrusion attempts, applies web filtering policies, and segments network zones to isolate critical systems such as student information systems and finance platforms.
Network segmentation is particularly important in education. By separating administration systems from classroom networks and guest Wi-Fi, schools reduce the risk of attackers moving laterally after an initial breach.
Endpoint and Device Security
With BYOD policies common across Australian schools, unmanaged devices present significant risk. Fortinet integrates with endpoint protection tools to ensure devices connecting to the network meet compliance standards.
Schools using Microsoft Intune for device management and compliance enforcement can integrate endpoint visibility into broader security monitoring. By combining endpoint posture checks with firewall policies, schools can automatically restrict access for non-compliant devices.
Secure Cloud and SaaS Applications
Most Australian schools operate in a Microsoft 365 environment, using Exchange Online, SharePoint, and Teams daily. While Microsoft provides strong native security controls such as Microsoft Defender for Office 365, network-level inspection remains essential.
Fortinet solutions enhance protection by
- Inspecting encrypted traffic to detect hidden threats,
- Preventing data exfiltration, and
- Enforcing granular application control.
Benefits of Fortinet Firewall Multi-Layered Security for Schools
Implementing a Fortinet firewall within a broader multi-layered security framework delivers tangible benefits for education institutions.
First, it reduces the risk of operational disruption. Ransomware attacks on schools can result in cancelled classes, data loss, and reputational damage. Integrated threat intelligence and automated response reduce dwell time and contain threats quickly.
Second, it improves visibility. IT leaders gain centralised reporting across network, endpoint, and application layers. This simplifies compliance reporting and audit preparation.
Third, it supports modern learning. Security must not hinder digital transformation. Fortinet’s high-performance architecture ensures secure access without slowing down cloud applications or video-based learning platforms.
Finally, it provides scalability. As schools expand campuses or increase enrolments, Fortinet infrastructure can scale without requiring a complete redesign.
Security and Compliance Considerations
Australian schools must comply with privacy obligations under the Privacy Act and manage sensitive student and staff data responsibly. A Fortinet firewall contributes to compliance by enforcing data loss prevention policies, maintaining detailed logs, and supporting secure access controls.
Regular firmware updates, threat signature updates, and configuration reviews are essential to maintain effectiveness. Technology alone does not prevent human error, so governance and awareness training must accompany technical controls.
Limitations and Risks
While a Fortinet firewall is powerful, it is not a standalone solution. Schools that deploy only a firewall without endpoint protection, identity management, or backup strategies remain exposed.
Performance misconfiguration can also impact user experience if SSL inspection or deep packet inspection policies are not tuned correctly.
Additionally, cybersecurity requires ongoing governance. Technology alone does not prevent human error. Staff awareness training and clear incident response planning must accompany technical controls.
This is why working with an education-focused partner such as Accucom is critical.
Why Fortinet Over Alternative Solutions?
Fortinet stands out due to its integrated Security Fabric architecture. Many competitors offer separate point solutions that require complex integrations. Fortinet’s approach reduces management overhead and improves cross-platform visibility, making it ideal for lean education IT teams.
Why Accucom
Accucom brings deep experience in Australian education environments, ensuring Fortinet deployments are tailored to school-specific needs. From firewall design and segmentation strategy to compliance alignment and ongoing optimisation, Accucom supports IT leaders at every stage.
If your school is reviewing its cybersecurity posture or planning a network refresh, speak with Accucom about implementing a Fortinet firewall as part of a robust multi-layered security strategy.
Contact Accucom today to discuss how we can strengthen your school’s cyber resilience while supporting modern, cloud-enabled learning environments.









 How Fortinet Firewall Multi-Layered Security Keeps Australian Schools Safe from Cyber Threats
How Fortinet Firewall Multi-Layered Security Keeps Australian Schools Safe from Cyber Threats